Most IT departments are asked to do a lot. From server support, PC support, to printer support and even application support, they have to wear many hats. Securing their wireless network is just one of those hats, a very critical hat but one of many none the less.
There are many requirements when it comes to your WLAN or RF design and having built-in security functions to protect your business from cyber threats. One of the most common wireless security threat is the rogue access point. Many times a rogue access point is created by employees wanting a faster internet connection or a nearby business wanting free WiFi.
The problem is that these routers try to connect to your wireless network and are typically installed in their default mode so authentication and encryption are not enabled —creating a pretty big security treat.
What are Rogue Access Points?
According to Michael McNamee, VP of Engineering at SecurEdge Networks, a rogue access point is, "Any access point that was not authorized by you to be placed on your network."
This tends to be a consumer-grade device that either an employee or an intruder purchases for wireless access to your corporate network and whether they have good intentions or not, it leaves your data vulnerable.

When to Suspect That an Access Point is "Rogue":
- The SSID of the access point doesn't match either your network SSID or any SSID on the permitted list.
- The access point is disguising itself as one of your SSIDs
- Normal network management features of the access point, such as SNMP, HTTP, and Telnet have been disabled.
- The access point's MAC address does not appear in the ARP tables.
- The access point has already been added by an administrator to the rogue access point list
- The access point could be operating as a bridge to another building, which has been configured for a wireless mesh
- The access point is an ad-hoc access point, formed directly between two client devices.
How Do Rogue APs Impact the WLAN?
Rogue access points and their clients undermine the security of an enterprise network by potentially allowing unchallenged access to the network by any user or client in the nearby area. Rogue access points can also interfere with the operation of your enterprise network.
Rogue access points and their clients undermine the security of an enterprise network by potentially allowing unchallenged access to the network by any wireless user or client in the physical vicinity. Rogue access points can also interfere with the operation of your enterprise network.
Rogue access points can impact your wireless network in many ways:
- They can create security holes in your network
- By allowing a hacker to conduct a "man-in-the-middle" attack, where the attacker makes independent connections with the victims and relays messages between them, making them believe that they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker.
- Send fake SSIDs advertising attractive features such as free Internet connectivity. Once a user connects, the fake SSID is added to the client’s wireless configuration and the client begins to broadcast the fake SSID, thereby infecting other clients
- Provide a conduit for the theft of company information
- They can negatively impacting your WiFi performance
- By imposing unmanaged RF contention or interference
- By flood the network with useless data, creating a denial of service
- If plugged in with a LAN instead of a WAN port, they can inject DHCP to the network which can cause problems
- When users try connecting to them thinking they are not valid access points and they cannot get to the proper resources due to VLAN differences, which can also generate a lot of help desk calls to your IT department
Why is Rogue AP Detection Important to Your WLAN Design?
Security should always be your first priority when it comes to your wireless network design. Since rogue access point detection is an important component in securing your wireless network, its vital that it be included from day one.
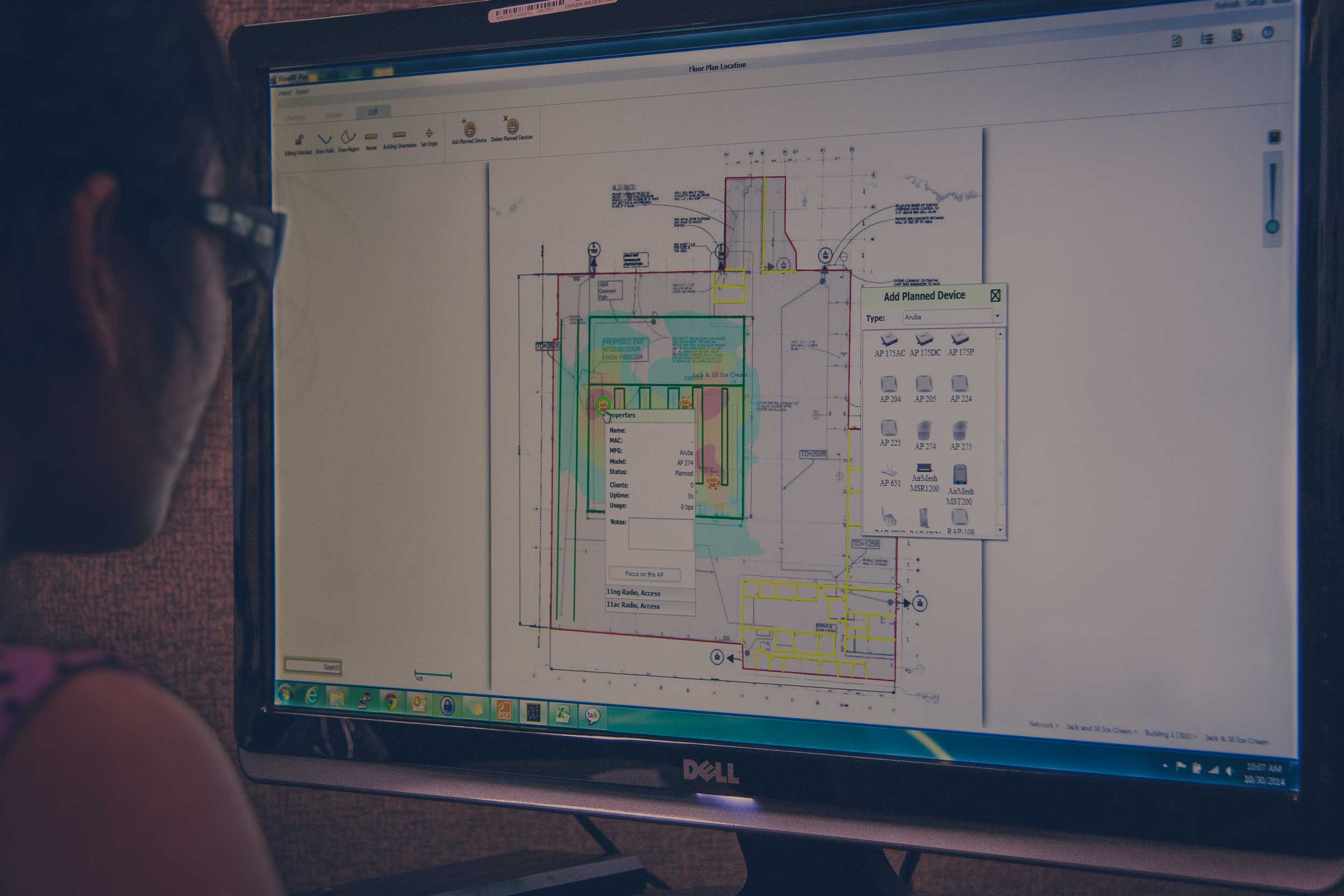
Rogue access point detection does two things, detection and mitigation. Whatever you decide to install on your network, it has to have the ability (from the beginning of your RF design) to be able to detect and mitigate rogue access points.
WLAN Design Basics
Not all wireless network designs are created equal, it's a skilled endeavor that requires a lot of training, experience, and performance testing to be done properly. Security should be at the foundation of every wireless design, and this means detecting access points that are rouge.
At SecurEdge, we deliver affordable, robust, and secure wireless platforms. We make sure that your wireless access balances security with a positive user experience. If you have any questions about wireless network designer would like to discuss an upcoming project, please contact us here.