While no one can accurately predict how many IoT devices will be in use over the next three years, (Gartner estimates around 20.8 Billion) the fact of the matter is there's going to be a lot. This raises many questions, but one of the most important is how will you secure those connected devices against security threats?
The internet of things offers an incredible wealth of opportunities, and for the early adopters some major competitive advantages as well. Here's a recent infographic that details how the internet of things is changing the world across a variety of industries.
However, there are many challenges that businesses and IT teams have to solve, to stay on the winning side of IoT, most notably, data security.
To shed some light on the topic of IoT security, here are four helpful tips businesses and organizations can use to keep their networks and end-users safe.
1. What security risks does the internet of things present?
IoT presents many inherit risks due to the nature of the embedded operating systems these devices possess. These operating systems are generally written for a specific function and security is not their primary focus and often times not even a consideration.
This oversight has resulted in security breaches using cameras, printers, environmental monitors and machine to machine controls. It seems there are weekly or even daily news reports of some company or home network being breached via an IoT device.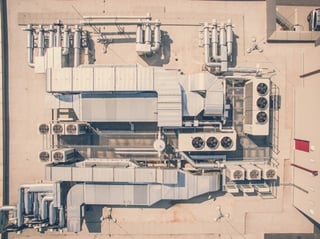
If you watch either the Homeland series on Showtime or Mr. Robot on the USA Network you would have seen some fictional, but not far from reality, example hacks of a Wi-Fi enabled pacemaker and HVAC controls.
2 How do you secure your wireless network when it comes to the Internet of Things?
Not including some semblance of security hardening of these devices is a gross oversight by the developers and manufacturers of these devices.
As a result when introducing these devices into an Enterprise environment there needs to be strict access control policies applied to eliminate or mitigate any potential for security breaches these devices can pose.
To accomplish this we believe the best method is to approach all systems from a security first mentality and build upon a flexible and adaptable security platform.
3 What features does your WLAN need to safely utilize the internet of things?
In our opinion we believe the WLAN needs the following features to safely allow the introduction and use of IoT devices;
- Firewall – IoT devices and their traffic have to be able to be integrated with a next-gen firewall from other segments of the network and the other host devices on those segments. This should be the first step in hardening the network for the hosting of IoT devices.
- Role based access – The WLAN has to be able to identify at some level what these IoT devices are, what they need and only provide them the absolute minimum resources for their functionality.
- Profiling – Each IoT device is going to have a specific function and a basic set of functionality requirements. It is imperative to have a profiling feature that identifies the device derived from a set of variables and behaviors and to leverage this to deliver a role assignment to these devices.
- IDS/IPS - The WLAN must incorporate some implementation of Intrusion Detection and Prevention in order to securely host IoT systems. The IDS/IPS system must be able to identify attacks or breaches from within and automatically blacklist or quarantine IoT devices or systems based on anomalous behaviors.
4 What are the most important things to consider when deploying the IoT?
Anyone deploying IoT devices into their network must perform some profiling of these devices or systems to have a better understanding of the risk vectors.
I would suggest the following inquiries to be made of the vendors or manufacturers about these devices or systems:
- What do these devices or systems need to access or communicate with?
- Do they need access to internal network hosted resources or are they simply an interface to report what they are connected to?
- Are the systems dependent on access to the Internet?
- Is remote access required across the WAN by service providers to these systems?
- Do these devices provide their own hosted access; Wi-Fi, Blue Tooth, or some other proprietary means?
- Do these devices have physical access means for programming or control; serial console or other cabled programming interface?
- Who internally needs to access these systems from the network and does their normal role include current access to the network?
- What security measures have the vendors or manufacturers implemented, if any, in their device or system.
Next Steps
The internet of things is only going to continue to grow and with it hackers and security threats will evolve right along with it. What has to change is our current approach to IoT security or rather lack there of for that matter.
From doing the simple things like changing manufacturer default passwords to the features listed here, network security isn't something to take lightly.
When it comes to network security, especially IoT Security, you're either secure or you're not.