Can you imagine going anywhere today and not having electricity? I know I can’t. Electricity is a fundamental utility that everyone—without any thought, expects to be available. Whether it’s a school, a bank, a hospital, a hotel, a warehouse, an office building or even your favorite restaurant, the idea of not having electricity just sounds ridiculous. Electricity is a mission-critical service, and like electricity, providing secure WiFi access has also become a mission-critical service.
However, for many, secure WiFi is still thought of as a luxury item—an afterthought that’s not valued as highly as other common utilities.
This way of antiquated thinking is really hard for me to make sense of and because of that, I felt it was necessary to discuss how secure WiFi has become a required, “must-have” utility for businesses of all shapes and sizes today.
So, read on—and find out what’s happened to transform how your business needs to approach wireless.
How things used to be
Oh how the times have changed. Since we started designing, deploying and managing enterprise wireless networks over 11 years ago, the wireless landscape has changed dramatically.
Back in the old days we designed networks very differently, dealing almost exclusively with Windows-based, Microsoft devices.
We deployed networks for environments where we controlled everything, in some cases even scanning each device that came onto the network. Unlike today, the wireless world was a much simpler, more predictable place.
Suddenly everything changed
On June 29th, 2007, the first iPhone (iOS device) was released and everything changed. Soon after, the first Android smartphone was released and no one looked back.
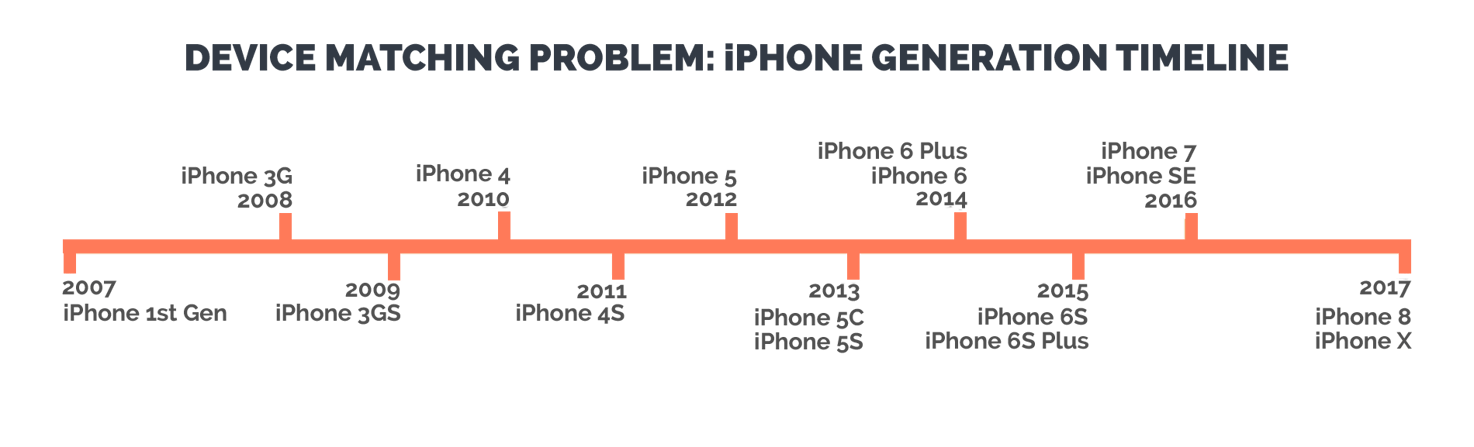
However, which device or platform came first is not what’s important, what’s important is how we thought about WiFi design and network security started to evolve.
Instead of owning every device that was accessing our networks and physically enforcing security on those devices, businesses and IT teams found themselves asking new questions. How do I control and secure devices that we don’t own?
How do we support and guarantee performance for growing numbers of devices and increasing types of devices?
How we use WiFi today
Flash-forward to today and 2007 seems like a century ago. Not only have the devices changed but the applications they run have changed, the RF environments have changed and the way businesses and people use wireless has completely changed.
Largely in part to the IoT, everything is becoming connected or going on-line. IT managers and CIOs are being asked to support and secure more and more devices through BYOD and 1:1 programs. Simply put, people are increasingly relying on wireless to work, live and play.

At SecurEdge for example, we rely on cloud-based applications and software that’s being hosted by Amazon or some other third-party to perform our day to day operations. If our WiFi network goes down or dips in performance, our entire company either struggles to keep operating or in the worst-case scenario comes to a complete stop.
And we’re not alone. Many other companies, large and small, have adopted this same or similar architecture that requires wireless access to properly operate.
We live in a culture where our end-users demand and expect fast, secure, always-on, wireless access. Where any interruption in performance, any breach in security (like a ransomeware attack)or any hiccup in the user experience will result in the following:
- Decreasing productivity
- Frustrated end-users taking to social media and review platforms to unleash their dissatisfaction
- and ultimately, lower revenue
At this point, the importance of secure WiFi should be nothing new, but the reality is, many businesses are still playing catch-up. As technology and the way we use wireless continues to evolve at a rapid pace, how do you plan to keep up?
What you can do to keep up
If you need electricity or you’re having problems with the power at your office building or at your hotel or school, do you install or try to fix it yourself?
Of course not, you partner with an experienced and certified electrician to get the job done right. So why should networking be any different?
Wireless systems are very complex to engineer and maintain. It takes a very specific skill-set which takes a lot of time and money to obtain—time and money that most businesses just don’t have.
To make things more challenging, mobile devices and other technologies operate on very short lifecycles, typically 12-18 months. After just two cycles these same devices will have completely changed, requiring a refresh of your wireless system.
The most you can expect to get out of your WiFi network is between 36 to 48 months.
To achieve the best results, you need four things:
- Your system needs to match the devices accessing it
- Plan for capacity
- Allow for both business and personal devices to coexist on the same network safely
- On-going monitoring of performance
What will it cost?
Traditionally, wireless has been thought of as a large one-time capital expense, and while there are some scenarios where this might still be an acceptable practice (at least for the hardware) it doesn’t make very much sense anymore.
Why spend a ton of money up front to only end-up with a network that’s obsolete in 3-4 years?
If you look at wireless as a “must-have” utility, like electricity, then it makes the most sense to purchase WiFi as a service or operational expense.
We call this solution, WiFi as a Service.
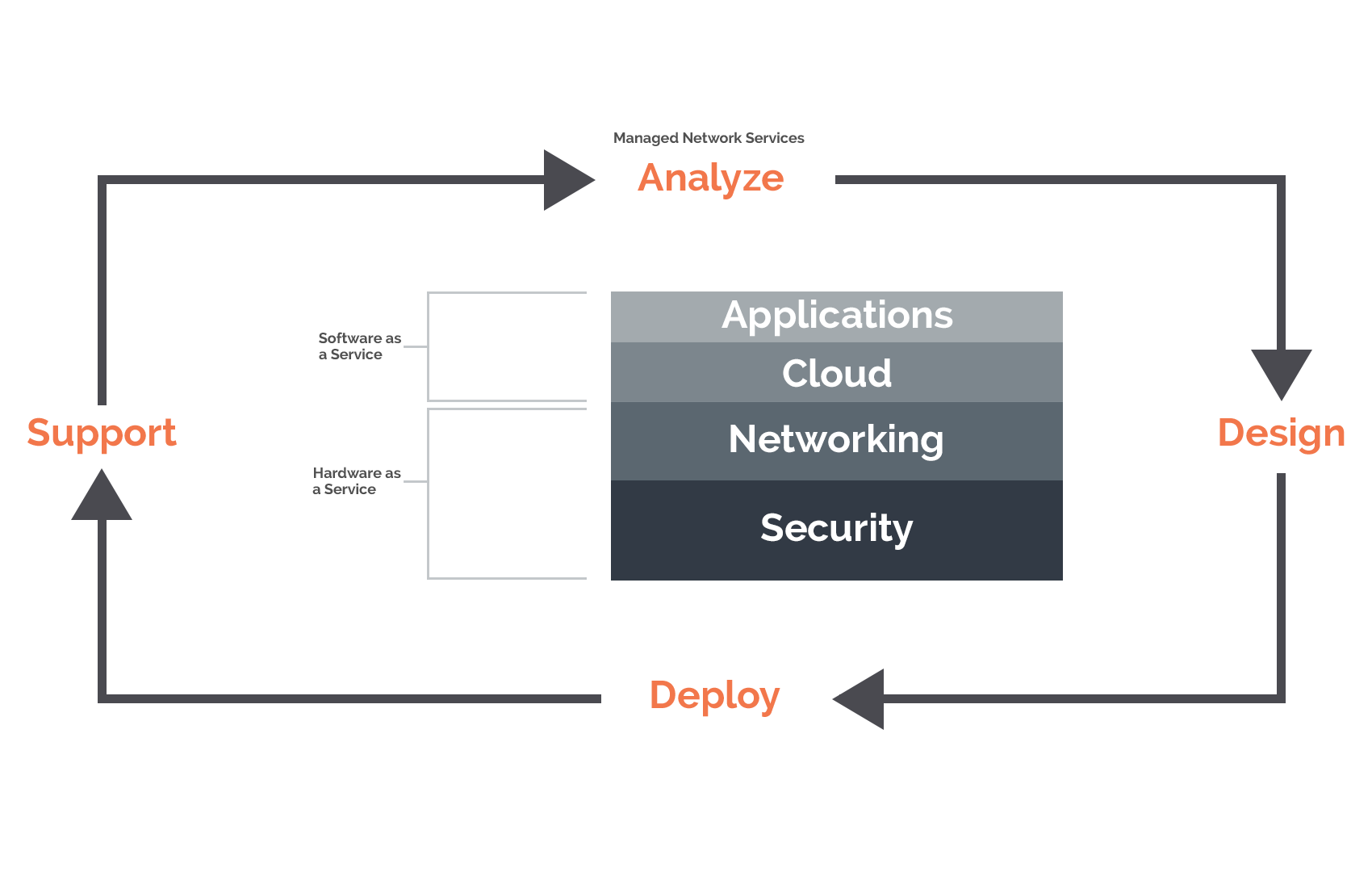
WiFi as a Service has many benefits including:
- Affordable monthly payments
- Scalable either up or down to fit your changing needs
- Guarantees performance SLAs
- Keeps your system up to date and aligned with your changing devices/applications
- Enables you to focus your capital towards other mission-critical needs
Ultimately, WiFi as a Service allows businesses to budget over time, exactly what it will take to deliver the best class of service for their end-users during a specific period of time.
Wireless used to be a luxury, but it’s safe to say that’s not anymore.
So—what does it cost? Check out our pricing page to find out what’s included, compare options and get started.