Whether it’s to send emails, track inventory, stream videos, or even save lives in hospitals, secure WiFi has become a mission-critical utility that helps run the world.
We’re living in an era where every industry requires wireless to support various requirements. Where your end-user’s demand WiFi access anywhere, at any time and on any device.
Deploying the infrastructure needed to provide secure WiFi access is both a complex and dynamic process.
How do you guarantee performance over-time? How will your business secure the devices it doesn’t own?
It doesn’t matter if you’re deploying WiFi for the first time or preparing to upgrade an existing network, here are 3 core elements that will help you deploy the fast, secure system your business requires.
1. Success comes down to the quality of your WiFi design
Proper WiFi planning and wireless network design takes extensive knowledge and years of experience to design, deploy and support a high-performing wireless system.
You can’t just purchase some access points turn them on and hope for everything to work without a hitch.
Successful networks are created using specialized WiFi design tools in the hands of experienced and certified engineers who have spent years mastering the specific skill-set needed to achieve the best results.
The right design tools
When you choose a partner to work with, they should have all the tools necessary to provide you with an extensive background as to what they are doing to test, build and secure your network.
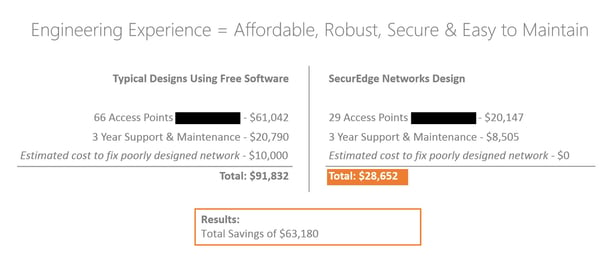
Do not buy into the idea of free predictive RF design software. When re-sellers, consultants or less experienced wireless service providers use this type of software it creates all kinds of headaches, from performance issues to cost.
Below is a graphic that illustrates a real deployment we were brought in to fix, demonstrating just how costly using the wrong tools can be:
 Experience and Certifications
Experience and Certifications
If you’ve ever set-up your own network in your home you could do it at your business too, right?
Wrong!
This is a very common mistake we’ve run into a lot and the reality is, commercial or enterprise networking gear is completely different than home networking equipment.
It takes years and a lot of money to train an engineer to the level necessary to properly design, deploy and support today’s wireless systems.
Your partner should be certified in the products they are installing, and if possible should have expert level certifications.
Experience is really the “X-factor” when it comes to getting your WiFi design right. We’ve been in business for over 11 years and with 1,000+ successful deployments under our belts in some extremely complex environments, we’re still constantly updating our processes and learning how to increase performance, security and reliability.
Wireless is a complex utility that is changing at an incredibly fast pace, to think anyone can do it is a fundamental mistake that will always come back to cost you in the long run.
2. Security needs to be the foundation of your network
Security is fundamental to the performance of your wireless system and your business. It should be the foundation your entire network is built upon.
There are two questions when it comes to security, “How do I secure the various types of devices on my network and how do I secure the devices I don’t own?”
Let’s take a look.
Various Types of Devices - IoT
With the Internet of Things gaining more and more traction, virtually everything is able to connect to wifi.
Generally, the operating systems for these types of devices are written for a specific function, and security measures are often loosely implemented or forgotten about all together, creating a higher risk for security breaches.
Your system needs to approach IoT with a security-first mentality, placing strict policies on these devices to decrease the potential for security issues.
Your business's WiFi design should include these elements to better prepare for the IoT:
- Integrated firewall
- Role-based access control
- Profiling
- Intrusion Detection and Prevention
Malware
In case you missed it a few weeks ago, a type of malware known as ransomware is on the rise.
Ransomware holds your data and files hostage, until a ransom is paid, if you don’t pay the ransom your business’s information is either released or simply deleted forever.
You should follow this multi-pronged approach that our VP of Engineering, Michael McNamee has outlined in this recent blog post, “Ransomware: What is it and how do you protect your business from an attack.”
Securing what I don’t own - Network Access Control
Mobile devices have changed the way we think about security today. There are two different scenarios now, either you own the devices and physically load something onto those devices to control them or in the case of BYOD, you control the behavior of those devices through security policies.
Network access control is one of the key components that allows you to control the behavior of your un-owned devices.
NAC allows you to see in real-time who, what, where, when and how your end-users are accessing the network. From there, you’re able to control what they can do and where they can go on the network based on pre-determined roles and security policies.
NAC is a game-changer when it comes to on-boarding devices and securing them and your network from malicious attacks. Ultimately network security is all about giving your end-users everything they need, nothing more and nothing less.
Check out this quick (less than 2 minute) video to learn more about the importance of Network Access Control:
3. Measuring performance
If you can’t measure the performance of your wireless network, how are you going to be able to know what’s causing poor performance? How will you be able to guarantee on an on-going basis that your end-users are getting the best experience possible?
Without measuring the performance of your wireless system from the perspective of your end-users, you can’t.
Expectations
Secure WiFi is no longer a “nice-to-have”. It’s time to look at wifi as a utility, a necessity that your business cannot operate without.
Failure to approach WiFi like you do with other utilities such as power can have very negative effects.
For example, students taking to twitter to rant about how their 30K a year tuition doesn’t seem to include reliable WiFi access or terrible hotel reviews from guests who can’t access the wireless while in their own room.
Expectations are only going to continue to rise, you need to invest in wireless as a required utility now to avoid consequences such as decreasing productivity, lower enrollment, and shrinking profits.
Wireless is a dynamic system
Your network is not a set it and forget it system, it’s alive and will need to be adjusted as you go, it’s a never-ending cycle of analysis and updates.
Everything is changing, from the types of devices and applications, to end-user usage and even the RF environment itself, you need a way of monitoring and managing your wireless system in real-time.
This is where a network management system steps in, giving you real-time visibility into various aspects of the overall health of your network as well as the experience your end-users are receiving.
Device Lifecycle
It’s critical to understand that your wireless network needs to align with the devices that are being used to gain access. Mobile devices have a 12 to 18-month lifecycle, which means the ideal lifecycle for your wireless system is between 36 and 48 months.
Your end-user’s devices need to be able to communicate with your WLAN, if your system is outdated things start to break down, and even if your end-users can connect, the wifi performance will continue to get worse and worse.
It’s not like buying a car where after 3-4 years and you’ve paid it off you still own a perfectly great car. Instead with technology after 3-4 years you own a glorified door-stop.
Next Steps
Wireless networks are complex and expensive, and often businesses don’t have the skill-set, time or budget to be specialized in wireless enough to properly handle those complexities.
WiFi as a Service provides a solution that allows businesses and organizations of any shape and size to simplify networking by purchasing the wireless infrastructure they need through a subscription.
This enables you to scale your system either up or down as you need and ensures your system is always on the cutting edge of technology.
Similar to other utilities, your wireless will be one simple monthly operating expense, freeing up capital for other mission-critical projects.
With a variety of packages available, deploying a fast, secure WiFi system has never been easier.