I hear it every day. A large fear and complaint about School Wireless Networks today is the need for more bandwidth as schools continue to adopt 1:1 and BYOD platforms.
One important way to conserve Internet bandwidth is have AGGRESSIVE measures in place to find and attack malware.
Malware can strip your organization of a tremendous amount of bandwidth. Many types of malware attempt to disable your system’s security features allowing control of the computer/device to be turned over. The bandwidth usage over time when these attacks are happening can add up quickly.
Cyber-attacks are advancing and engaging persistent methods to sidestep conventional security measures. Modern security teams are left to re-evaluate their basic assumptions that traditional intrusion prevention systems, antivirus and single-purpose sandbox appliances are up for the assignment of suppressing these advanced persistent threats (APT’s.) To support forceful malware analysis across the entire network a cloud-based architecture can analyze large numbers of potentially malicious content without having to deploy single-use hardware at every single ingree/egress point and network point of existence.
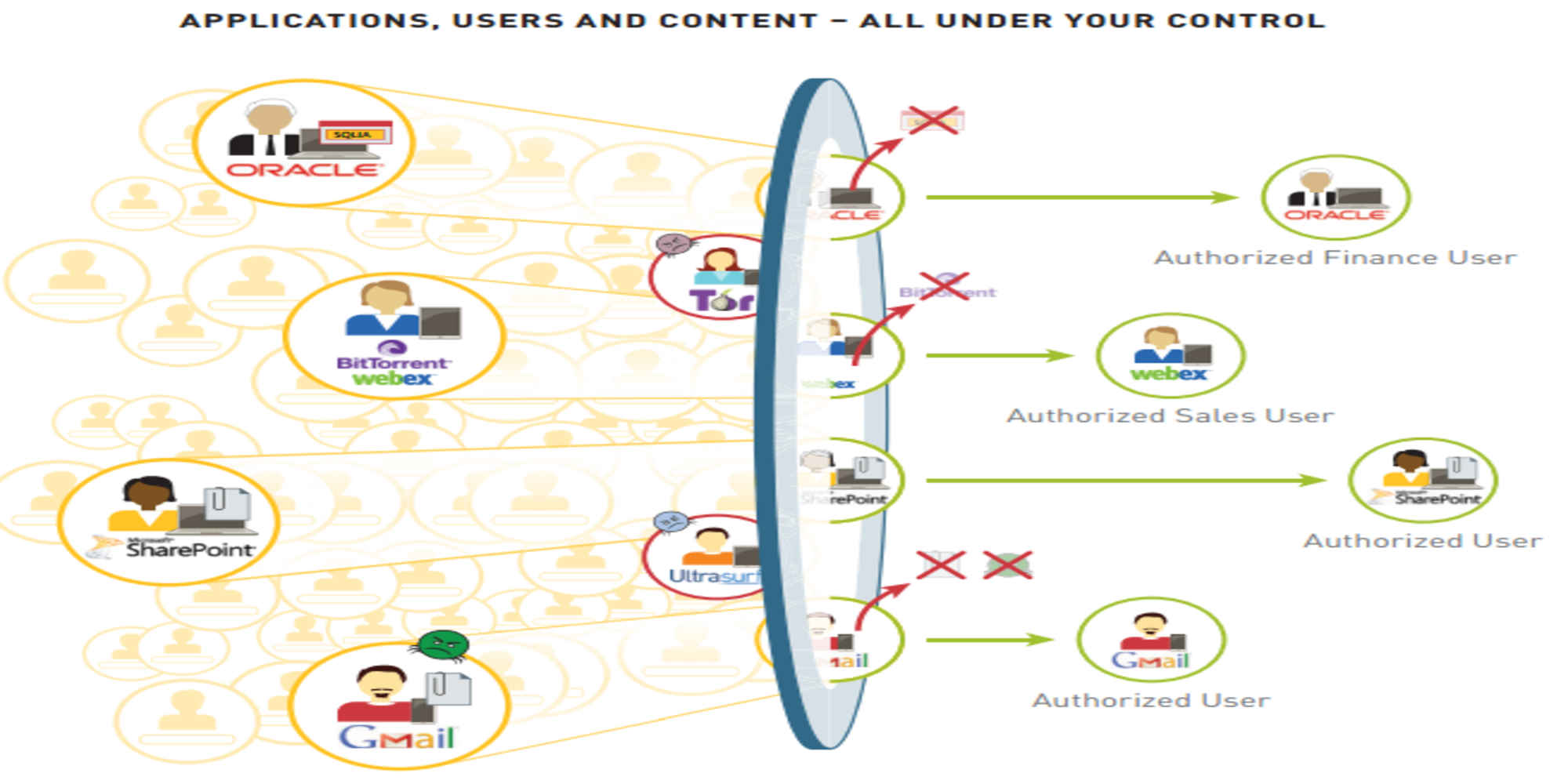
A Palo Alto Next Generation Firewall allows for a public or private cloud deployment and this virtual malware analysis can be shared across all firewalls without the requirement of extra hardware. This virtual protection detects the threat but then protects the users and networks by:
- Blocking the threat across the cyber-kill chain and using behavioral analysis to identify exploits in common applications and operating systems, sharing the update with all the subscribers in as little as 30 minutes.
- Thoroughly looking into the malicious outbound communication to disturb command-control activity causing future attacks on the network to be halted.
- Seeing and filtering operating systems and applications (encrypted or not) including PDF’s Office Documents, Java and APK’s
- Visibly, in a single view, giving administrators information on malware, it’s behavior, and compromised hosts so response time can be quick allowing proactive controls to be built.
With these detections at each step of the attack lifecycle the number of threats that penetrate an organization can be dramatically reduced as well as much need bandwidth can be used for its proper function; allowing our students to use technology safely and securely to learn.
If you would like a free demo or have further questions contact us here.