Education must adjust to better accommodate the way students learn today, and for today’s students that includes the use of technology. Wireless technology in the classroom is becoming an increasingly significant part of learning these days. As great as it is for students and teachers, it can cause nightmares for the school IT staff, because it does create an inherent wireless network security risk.

To help your schools IT staff get a better night’s sleep and make sure your school is secure and safe for all users, Palo Alto Networks next-generation firewall can help. They offer a complete, all-in-one solution that is very easy to use and manage.
Today’s school wireless networks need a way of gaining greater visibility of what is being accessed, as well as greater control over the specific applications that students will be or already are accessing.
Schools must also comply with CIPA (Children’s Internet Protection Act), which is a federal law enacted by the United States’ Congress to address concerns about access in schools and libraries to the Internet and other information. CIPA requires schools to have web filtering, monitor online activities of students, and other safety policies.
Rene Bonvanie, vice-president of worldwide marketing at Palo Alto Networks, said: “We have had tremendous success in the education sector precisely because we enable organizations to effectively balance the need for both access and security.
“Unlike legacy security technologies, our next-generation firewalls are unique in their ability to see and control applications, users and content – not just ports, IP addresses and packets.”
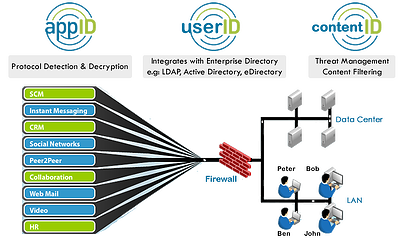
Palo Alto Networks’ next-generation firewall uses three innovative technologies that allow schools to get visibility and control over applications, users, and content navigating their network. App-ID, User-ID and Content-ID, bring the applications, users, and content under policy control using high performance firewall architecture.
App-ID
Schools must filter applications and internet traffic to protect those little eyes and ears. State and Federal regulations, school board policies, community standards, and common sense pretty much require it. App-ID technology identifies applications regardless of port, protocol, evasive tactic or even SSL encryption, all at up to 20Gbps with no performance degradation.
App-ID can help control today’s tech-savvy students who are progressively using a new class of application that can easily sidestep current security mechanisms such as firewalls, URL filtering and proxy servers.

User-ID
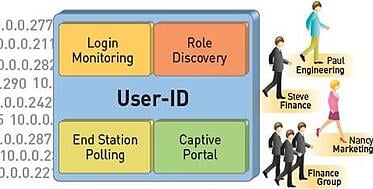
User-ID is a technology that integrates Palo Alto Networks next-generation firewalls and your schools’ active directory, providing visibility and control of applications based on users and groups – not just by IP addresses.
This way you can control applications based on the user and group information from active directory. You obviously don’t want students to have access to everything the teachers have access to. Student policies can be different than Faculty, Administration, or even IT.
Content-ID
Content-ID is a content inspection appliance that prevents a wide range of threats, blocks unauthorized file and data transfers, and controls web surfing. It provides a real-time threat prevention engine, combined with a comprehensive URL database, and elements of application identification.
Content-ID allows schools to manage Internet access to prevent the possibility of inviting, infecting, and corrupting users on the school wireless network.

Palo Alto Networks next-generation firewalls can help schools protect their network, students, and other users as well as maintaining CIPA compliance. That’s why every school wireless network needs Palo Alto next-generation firewall. If you have any questions or would like a free demo, contact us here. Download the eBook below as a great resource.






